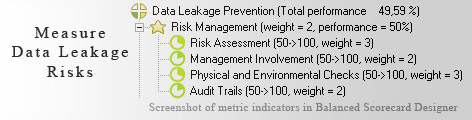
 Data Leakage Prevention is one of the most important security functions for any organization in today-s world. KPIs in this regard help to analyze the security systems of organizations in order to prevent probable loss of sensitive data.KPIs in Data Leakage Prevention are grouped under four major categories-Risks Management, Security Control, Authorized Processing and Data Integrity.Risk Management speaks about the actions taken by the business to reduce risk associated with data leakage. It considers KPIs like Risk Assessment, Management Involvement, Audit Trails and Physical and Environmental Checks.Security Control perspective measures the steps taken by the business to improve the security aspect of the systems. It comprises of KPIs such as Compliance level, Tracking Effectiveness, System Security Plans and Encryptions.Authorized Processing includes KPIs like Authorization, Interim Authority to Operate (IATO), Background Screening and Interception Protection. These indicators ensure that the data is accessible only to the right persons. Data Integrity means maintaining the originality and individuality of the data important to the organization. It represents KPIs such as Virus Scans, Password Verification, Unique Users IDs and Logical Controls.
Data Leakage Prevention is one of the most important security functions for any organization in today-s world. KPIs in this regard help to analyze the security systems of organizations in order to prevent probable loss of sensitive data.KPIs in Data Leakage Prevention are grouped under four major categories-Risks Management, Security Control, Authorized Processing and Data Integrity.Risk Management speaks about the actions taken by the business to reduce risk associated with data leakage. It considers KPIs like Risk Assessment, Management Involvement, Audit Trails and Physical and Environmental Checks.Security Control perspective measures the steps taken by the business to improve the security aspect of the systems. It comprises of KPIs such as Compliance level, Tracking Effectiveness, System Security Plans and Encryptions.Authorized Processing includes KPIs like Authorization, Interim Authority to Operate (IATO), Background Screening and Interception Protection. These indicators ensure that the data is accessible only to the right persons. Data Integrity means maintaining the originality and individuality of the data important to the organization. It represents KPIs such as Virus Scans, Password Verification, Unique Users IDs and Logical Controls.
Read Why do business professionals choose ready-to-use KPIs? to find out the answers to these questions:
Ideally, you need to have a strategy (in a form of a strategy map) before you start thinking about the ways to measure its execution (KPIs). Don't have a strategy map yet? Use free Strategy Map Wizard to create a strategy map for your current business challenges. The wizard will:
The whole process takes on average 6 minutes. Give it a try right now - it's free.
Data leakage is one of the most plausible harm that has come along with the IT age. Most organizations are ready to do anything to stop such unauthorized flow of data. Though success has been met with implementation of security measures, complete elimination of data stealing still remains an evolving branch.
There can be innumerable entities, both from the internal and external environment who have been vying for 'illegal procurement of data'. However, this has to be prevented as data movement that does not confirm to the organizational rules is both risky and dangerous.
The key is to bring sophisticated and complicated 'locks' and 'barriers' into pictures so that data access by non-prescribed entities is successfully kept to minimum.
This has double advantage for users as it not only helps in keeping information flow 'restricted' but also ensures that right information reaches the right person, the latter being an outcome of safe compartmentalization of databases.
The issue emphasizes for having a methodology to count the efforts and attempts being made to tackle 'un-allowed' data movement. Saying it all, one can terminate the instances of data stealing by limiting the access to databases.
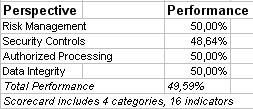
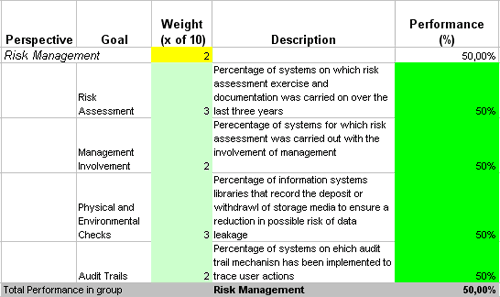
This is the actual scorecard with Data Leakage Measures and performance indicators. The performance indicators include: data leakage prevention, risk management, risk assessment, management involvement, physical and environmental checks, audit trails, security controls, compliance level, tracking effectiveness, system security plans, encryption, authorized processing, authorization, iato, background screening, interception protection, data integrity, virus scans, password verification, unique user ids, logical controls .
Download a trial version of Data Leakage Estimation Balanced Scoreboard or purchase a full version online.
How is this book different from 796 other book titles about KPIs on Amazon?
"Before writing a single line, I formulated some guiding principles, one of them was: "If our clients ask, "How can I find a good KPI for..." - I want this book to provide a perfect answer."