 The underlying cause of the identity theft crime wave is the very nature of our digital economy, making it an extremely difficult problem to solve. Most people's personal data is in literally thousands of systems, potentially accessed by tens or hundreds of thousands of people. However, it's important to recognize that above and beyond the risks to individuals, government and business organizations have a newly emerging and substantial liability specifically for theft of employee identities, and that an organization's HRIS management has a critical role to play in mitigating this threat.
The underlying cause of the identity theft crime wave is the very nature of our digital economy, making it an extremely difficult problem to solve. Most people's personal data is in literally thousands of systems, potentially accessed by tens or hundreds of thousands of people. However, it's important to recognize that above and beyond the risks to individuals, government and business organizations have a newly emerging and substantial liability specifically for theft of employee identities, and that an organization's HRIS management has a critical role to play in mitigating this threat.
Read Why do business professionals choose ready-to-use KPIs? to find out the answers to these questions:
Ideally, you need to have a strategy (in a form of a strategy map) before you start thinking about the ways to measure its execution (KPIs). Don't have a strategy map yet? Use free Strategy Map Wizard to create a strategy map for your current business challenges. The wizard will:
The whole process takes on average 6 minutes. Give it a try right now - it's free.
Identity theft has been increasingly creating a mess with people who are active users of digital world services. People would suddenly get to know their bank accounts have run out of funds and that they are under heavy debts.
In other words, this personification has come up as an ugly 'side-effect' of electronic mode of operations.
Looking at the subject, it is discovered that there are two types of identity thefts are recognized- Account takeover and application fraud.
Account takeover occurs when the thief buys products and services using the credit card as such or through the expiration date and account number from it.
Moving ahead, application fraud or 'true name fraud' is when the stealer uses SSN number and opens accounts in your name.
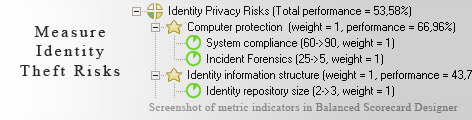
Prevention of identity theft requires being cautious when handling information to others. However, escaping from this possible trouble is an extremely difficult job as a constant monitoring may not be possible at times. However, balanced scorecard can be employed to keep an eye on this danger in sufficient details. One can spot the needed metrics and frame those under useful categories to get rid of the worries.
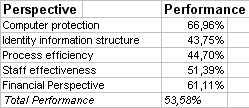
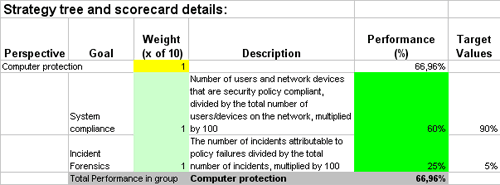
This is the actual scorecard with Identity Theft Risks Indicators and performance indicators. The performance indicators include: balanced scorecard, provisioning process coverage, authorization claims.
Download a trial version of Identity Theft Risks Evaluation Balanced Scoreboard or purchase a full version online.
How is this book different from 796 other book titles about KPIs on Amazon?
"Before writing a single line, I formulated some guiding principles, one of them was: "If our clients ask, "How can I find a good KPI for..." - I want this book to provide a perfect answer."