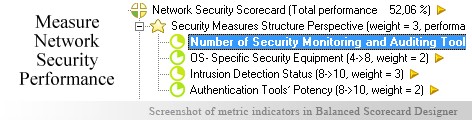
 KPIs in Network SecurityIt is necessary to regulate the information flow within a given network (in simpler cases) and between networks (in complicated ones) to make sure that only the right piece of information reaches the right user. This demands looking after a number of aspects for achieving an overall performance. The areas in this respect are- Security Measures Structure, Internal Operations, Network Structure and Mechanisms Performance Perspective. Moving into details, the KPIs for having Security Measures Perspective are- Number of security monitoring and auditing tools, OS- specific security equipments, Authentication Tools' potency and Intrusion Detection Status.Internal Operations can be had with KPIs like 'Security Policy Compliance', 'Network Coverage ratio', 'Devices and equipment investment' and 'Updates Frequency'. A suitable structure for Network can be created using metrics such as 'Node synchronization degree', 'Password Frequency change', 'Frequency of Security Tests' and 'SUS Potential'.Finally, the Mechanisms Performance can be analyzed using KPIs 'Drop in Data Leakage Instances', 'security awareness ratio', 'Feedback Degree' and 'Pre: Post security mechanisms scenario'.
KPIs in Network SecurityIt is necessary to regulate the information flow within a given network (in simpler cases) and between networks (in complicated ones) to make sure that only the right piece of information reaches the right user. This demands looking after a number of aspects for achieving an overall performance. The areas in this respect are- Security Measures Structure, Internal Operations, Network Structure and Mechanisms Performance Perspective. Moving into details, the KPIs for having Security Measures Perspective are- Number of security monitoring and auditing tools, OS- specific security equipments, Authentication Tools' potency and Intrusion Detection Status.Internal Operations can be had with KPIs like 'Security Policy Compliance', 'Network Coverage ratio', 'Devices and equipment investment' and 'Updates Frequency'. A suitable structure for Network can be created using metrics such as 'Node synchronization degree', 'Password Frequency change', 'Frequency of Security Tests' and 'SUS Potential'.Finally, the Mechanisms Performance can be analyzed using KPIs 'Drop in Data Leakage Instances', 'security awareness ratio', 'Feedback Degree' and 'Pre: Post security mechanisms scenario'.
Read Why do business professionals choose ready-to-use KPIs? to find out the answers to these questions:
Ideally, you need to have a strategy (in a form of a strategy map) before you start thinking about the ways to measure its execution (KPIs). Don't have a strategy map yet? Use free Strategy Map Wizard to create a strategy map for your current business challenges. The wizard will:
The whole process takes on average 6 minutes. Give it a try right now - it's free.
Network Security is of utmost importance to organizations as this aspect determines the 'amount' and 'direction' of information flow.
'Information', as has been found is the strongest support of a firm as chances of decisions turning 'fruitful' depends on how much information the seeker can lay hands on, at any given instance.
Concluding from this, one gets that any compromise or slack in this subject of Network safety can create huge problems for the organization. This area is concerned with constructing concrete 'technical boundaries' around the 'information pool'.
Also, the efficiency of IT department can be largely determined from the degree of 'security the organizational network has'. The approach often adopted by managers is bi-directional in nature- 'constructing a suitable network infrastructure' and 'coming up with a related group of policies' with a common aim of making sure that no 'unauthorized element manages to jump the safety measures'.
This makes it mandatory enough to initiate a search for an efficient performance management tool. Often organizations have found an answer to this question in the form of Balanced Scorecard. This is used for collecting together the KPIs (Key Performance Indicators) that matter to the organizational progress or growth. By packing these indicators together, one can effectively look forward to organizational network security management.
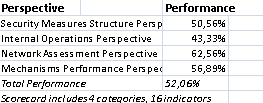
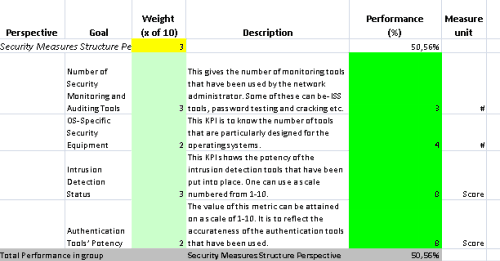
This is the actual scorecard with Network Security Performance Indicators and performance indicators. The performance indicators include: security measures structure perspective, number of security monitoring and auditing tools, os- specific security equipment, intrusion detection status, authentication tools’ potency, internal operations perspective, security policy compliance, network coverage ratio, updates frequency, equipment and devices investment, network assessment perspective, node synchronization degree, frequency of password change, sus potential, frequency of security tests, mechanisms performance perspective, drop in data leakage instances, pre: post security mechanisms scenario, feedback degree, security awareness rise.
Download a trial version of Network Security Evaluation Balanced Scorecard or purchase a full version online.
How is this book different from 796 other book titles about KPIs on Amazon?
"Before writing a single line, I formulated some guiding principles, one of them was: "If our clients ask, "How can I find a good KPI for..." - I want this book to provide a perfect answer."